Multi-site growth rarely fails because teams lack skill. It fails because variation multiplies faster than governance. A new branch inherits a slightly different VLAN plan. A warehouse gets an extra SSID “for testing” that never goes away. A firewall rule changes at one site to fix a local issue and never makes it back into the standard. Within months, the environment becomes a patchwork. Troubleshooting slows down because engineers spend time learning each site’s quirks instead of solving the incident. Audit prep becomes a scavenger hunt across exports, screenshots, and tribal knowledge. The operational burden grows faster than the site count, especially when the same team supports switching, wireless, and security across dozens or hundreds of locations. This is the point where centralized network management stops being a preference and becomes a requirement for uptime and control.
Meraki templates address that operational problem by changing what you manage. Instead of treating each site as a one-off project, templates let you manage patterns: standard SSIDs, VLAN structures, security baselines, and switch port behavior that should look the same everywhere. In the Meraki dashboard, templates become a governance layer that keeps sites aligned even as devices change, staff rotates, and regions expand. A template-driven model makes scale predictable because it replaces ad-hoc change with controlled, repeatable configuration. Stratus Information Systems supports organizations designing Meraki environments where scale does not compromise control.
Meraki emplates sit at the organization level in the Meraki dashboard, which matters because the organization is where you define shared intent: licensing, admin roles, global inventory, and the baseline standards you want to replicate. Networks live under an organization and typically represent a site, a campus segment, or an operational domain. Templates act as reusable configuration containers that can bind to many networks at once. Conceptually, a template is the “gold standard” network definition, while the bound networks are the site instances that inherit that standard. This hierarchy becomes a force multiplier in large environments. It gives architects a place to define guardrails, gives operations teams a predictable structure to support, and reduces the risk that a new site launches with an improvised configuration.
Operationally, this model keeps responsibility clear. A central team can own templates and baseline policies. Regional teams can own site readiness and local constraints. Support teams can troubleshoot within the boundaries of known standards. When structure matches how teams work, the dashboard becomes easier to navigate and incidents become easier to triage. The result is not only faster deployments. It is a cleaner operational model that stays workable at 20 sites and still works at 200.
Binding is where templates become real operations. When a network is bound to a template, the settings controlled by the template become centrally managed. That usually includes the baseline configuration you want to keep consistent across locations: wireless SSIDs and authentication methods, security and traffic shaping policy, switch port profiles, and other repeatable standards. The exact scope depends on what you build into the template, but the outcome is consistent: configuration ownership shifts upward from the site to the template for those template-managed areas.
This does not remove local visibility. Site teams still see their network, devices, clients, and local health. They can still troubleshoot, monitor, and handle site-specific tasks that should remain local, such as naming conventions, local subnets, circuit identifiers, or a local printer segment. The important part is that the core standards stop being rewritten at each site. Support workflows improve because “normal” becomes consistent. When a ticket comes in, engineers spend less time validating what should exist and more time resolving what changed. Over time, the environment develops a stronger signal-to-noise ratio because the dashboard reflects intended design rather than accumulated exceptions.
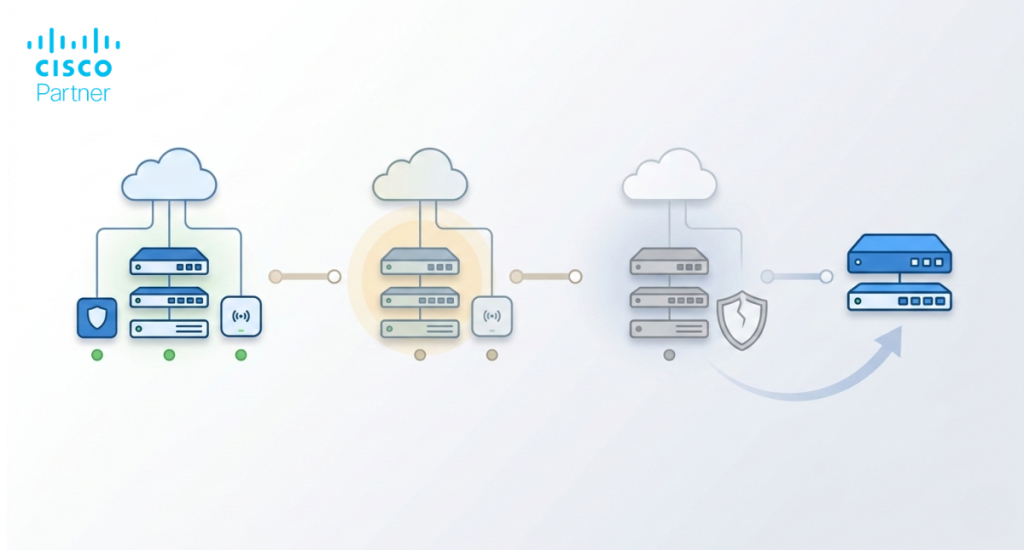
Templates are the right tool when you want long-term consistency. A template-bound network stays connected to the standard, which means baseline updates can be applied across many sites without repeating the same work. This is ideal for distributed branch environments, retail chains, clinics, schools, and any model where you want site behavior to be predictable and uniform.
Cloning is better when you need a one-time copy of a known-good configuration, but you do not want ongoing coupling. Cloning is useful for special-purpose sites, labs, or unique environments where standards are shared at launch but diverge intentionally later. It also fits teams that prefer to “freeze” a config as a starting point and then manage deviations deliberately.
Automation, typically via APIs, complements both models. APIs can validate standards, generate reports, and orchestrate deployment workflows. In template-heavy environments, automation often focuses on assurance: drift checks, inventory reconciliation, and change reporting. In clone-first environments, automation often drives build and lifecycle actions per site. The key decision is governance. Meraki templates anchor centralized network management by making standards persistent. Cloning and automation become effective when they are used in a disciplined model rather than as substitutes for structure.
A template strategy should map to operational patterns, not the number of locations. The fastest way to create template sprawl is to build a new template for every site category that feels slightly different. Instead, define a small set of archetypes that match how your business operates. Common archetypes include a standard branch office, a larger regional office, a warehouse or distribution site, a campus building, and a high-control environment such as a manufacturing floor or regulated lab. The archetype should reflect consistent needs: user density, wireless requirements, segmentation, uplink patterns, and the level of standardization expected.
Functional similarity matters more than geography. A branch in London and a branch in Chicago can share the same template if their role are the same and their baseline security and segmentation needs match. If you separate templates by region without a functional reason, you increase maintenance overhead and create drift risk. A tight template catalog keeps your environment governable. It also helps with training. New engineers learn a handful of patterns instead of reverse-engineering dozens of one-off designs.
A strong template defines what must be consistent and what can vary. Put the baseline architecture into the template. That usually means VLAN structure standards, SSID and authentication design, firewall and content filtering baselines, and traffic shaping policy. Switch port profiles and common uplink behaviors also belong here, especially if you want consistent edge access for phones, printers, cameras, and APs.
Keep site-specific parameters out of the template when they would force exceptions. Local subnets often vary by site, especially when IP plans are allocated per location. Circuit details, local ISP handoffs, and locally required devices may require per-site tweaks. The goal is to standardize the “shape” of the network and the security posture while keeping legitimate local constraints manageable.
This boundary definition is where many deployments succeed or fail. If you try to template every parameter, you create friction and exceptions. If you template too little, you lose the operational benefit and drift returns. Aim for standards that reduce variance and simplify support, not standards that force every site into an unnatural design.
IP planning becomes more important once templates are in play, because a template-driven environment scales quickly and magnifies addressing mistakes. Each bound network typically needs unique subnets, even when the VLAN structure is standardized. That means you need a repeatable method for allocating address space per site and documenting it in a way that operations can rely on. Common patterns include allocating a contiguous block per site, using a predictable site ID scheme, and reserving dedicated ranges for voice, corporate, guest, and IoT segments.
If you use Auto VPN, plan for how site subnets will be advertised and how traffic will flow. A consistent subnet scheme reduces routing confusion and supports clean segmentation across sites. It also improves change control. When a site is added, the network team can predict where it fits into the routing model, how to apply policies, and what should be reachable. When subnet planning is inconsistent, VPN policy becomes harder to reason about, and troubleshooting becomes slower because routes do not follow predictable patterns.

Start with a proven design, not a blank page. The best base templates usually come from a stable pilot network that already reflects your intended standards. The work is in removing site-specific exceptions. Strip out one-off VLANs, odd port overrides, and temporary SSIDs. Convert ad-hoc changes into deliberate policy. The goal is a clean template that represents how you want new sites to operate.
Validation should be practical and repeatable. Test onboarding a new network and binding it. Confirm VLAN behavior, SSID functionality, authentication flows, and firewall enforcement. Validate switch port profiles across common endpoints. Confirm that monitoring and alerting behave as expected. If you use Auto VPN, validate the route advertisement and traffic policy in a controlled scenario. A base template that looks correct but has not been exercised will cause painful surprises when you bind dozens of sites.
A good practice is to document the “template contract.” Define what the template guarantees: SSIDs, VLAN naming and purpose, baseline security posture, and standard port profiles. That document becomes a reference point for operations and a safeguard against gradual erosion.
With Meraki templates, you can apply changes to many sites at once. That is the advantage and the risk. Treat template edits like code changes with a blast radius. Use staging networks to test changes before pushing them to production. Maintain a pilot group of sites that receive template updates first, then expand the rollout once validation is complete. Peer review matters here. A second set of eyes catches mis-scoped rules, inconsistent VLAN changes, or SSID updates that could break authentication at scale.
Rollout sequencing should reflect business impact. Start with low-risk sites or sites with on-site support. Avoid pushing major template changes during peak business hours across every region. Document a rollback plan before you change anything. That plan can be as simple as knowing the prior settings, the affected networks, and the fastest path to revert. The biggest operational win is not speed. It is confidence that the environment stays stable as you improve standards.
Exceptions are inevitable. The goal is to keep them rare, justified, and visible. If a site needs a special VLAN for a local system, document it and track it as a controlled deviation. Avoid “temporary” overrides that become permanent. Review exceptions on a schedule. Quarterly is a practical starting point for large environments. Ask two questions: does the exception still exist, and should it become part of the standard template.
When exceptions become common, the template likely needs refactoring. Either your archetype definition is wrong, or your standardization boundaries are too strict. That is not a failure. It is feedback from real operations. The risk is allowing exceptions to accumulate without governance. Over time, that recreates the drift problem you used templates to solve.

Templates shine during site turn-up. Pre-stage the network in the dashboard, bind it to the correct template, and claim devices into the network before they ship. When equipment arrives on-site, the local task becomes physical: rack, power, and connect uplinks. Configuration pulls down automatically once devices check into the cloud. This reduces reliance on on-site specialists and shortens rollout cycles.
Pre-staging is not only about speed. It removes uncertainty. If the site goes live with the correct SSIDs, VLANs, and security baselines, you reduce the chance of a “soft launch” where the network runs in a partially configured state for days. That partially configured state is where incidents and audit gaps often originate. A template-driven approach makes the first boot a compliant boot, provided your template is clean, and your site instructions cover cabling, power, and ISP handoff requirements.
A template-bound fleet is easier to support because engineers know what “normal” looks like. When an issue occurs, you can quickly compare a problematic site against the standard configuration and against other sites bound to the same template. This reduces ambiguity. Instead of asking, “Is this site configured differently?” you can focus on “What changed?” or “What local condition is causing variance?”
Meraki templates also reduce the need for manual configuration audits. Support teams spend less time hunting down mismatched SSIDs, inconsistent trunk settings, or one-off firewall rules. They can concentrate on signal quality, circuit stability, client behavior, and application performance. Incident response improves because troubleshooting steps become repeatable across locations. That repeatability is a real operational asset, especially when teams support many regions with limited staff.
Audit readiness improves when standards are enforceable and reviewable. Templates help you demonstrate that baseline controls are consistent across sites and that changes are intentional. Instead of collecting evidence site by site, you can show the template as the baseline and document the binding across locations. That reduces the time and complexity of preparing for reviews.
Templates also help enforce accountability. Changes to a shared baseline require deliberate action, which encourages peer review and change logging. Over time, this produces cleaner evidence trails because fewer changes happen through local improvisation. It does not eliminate compliance work. It reduces operational gaps that lead to audit findings, such as undocumented variance, inconsistent security policies, and unclear ownership of configuration standards.

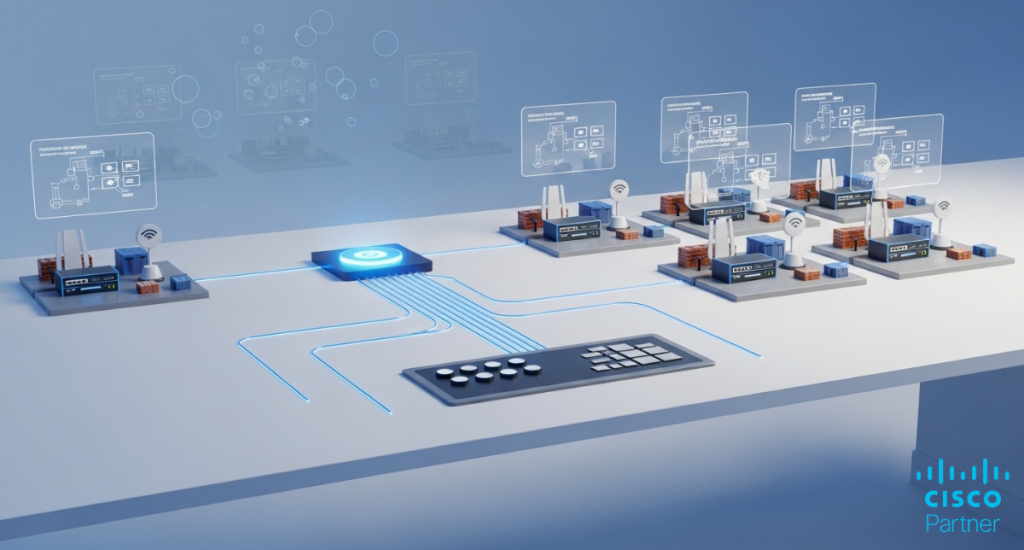
Many organizations derive the greatest value by standardizing across product families through a unified template approach. A branch archetype often includes a security appliance for edge and VPN, switches for access and uplinks, wireless access points for client connectivity, and optional cellular gateways or sensors for resilience and telemetry. When these components share a template-driven baseline, new sites come online with consistent segmentation, SSID behavior, port profiles, and security posture.
Coordination matters. Wireless VLAN mappings must align with switch trunk settings. Security policies must match the segmentation model. Uplink design must reflect the WAN and VPN strategy. Unified templates force you to design these dependencies deliberately, which is a benefit. It reduces the risk of “wireless is ready but switching is not” or “VPN is up but the VLAN policy is wrong.” For multi-site operations, consistent cross-domain design often matters more than perfect device-level tuning.
Templates are not mandatory for every environment. Highly specialized sites may require independent control and slower change cycles. Data centers, labs, and test environments often benefit from isolation because they change frequently or have unique requirements that do not map well to standard archetypes. In those cases, cloning a known-good baseline and then managing the site independently can be more appropriate.
Templates can also become a poor fit if the organization cannot support disciplined change control. A template-driven model requires governance. If multiple teams edit templates without coordination, you can create fleet-wide instability quickly. The tool is powerful. The practice must match the power. For environments that cannot maintain a central template owner model, a hybrid approach can be safer: templates for core branch archetypes, clone-first for special sites, and automation for validation across both.
APIs complement templates by adding assurance and reporting. A common approach is to use API-based checks to confirm that bound networks remain aligned with standards and that exceptions are visible. Drift detection scripts can flag unexpected SSIDs, VLAN anomalies, or device placement errors. Reporting scripts can generate dashboards for leadership: site readiness, template adoption rate, exception counts, and change activity.
Automation can also support lifecycle operations. When a new site is created, scripts can apply naming conventions, tags, admin scopes, and documentation records. When a site is decommissioned, automation can remove bindings, reclaim inventory, and ensure records are updated. The goal is not automation for its own sake. It is reducing manual steps that create inconsistent outcomes. Templates provide the baseline. APIs help you enforce and measure it at scale.
Meraki templates bring operational order to multi-site growth. They reduce drift by turning standards into an enforceable configuration, not documentation that nobody reads. They speed up deployment because new sites inherit known-good patterns. They improve troubleshooting because behaviour becomes predictable across locations. They make operations more reliable because change control can be centralized and staged. Over time, a template-driven model becomes the practical foundation for scalable centralized network management, especially in organizations where the network supports revenue workflows, safety requirements, or regulated operations.
Stratus Information Systems helps organizations design Meraki template strategies that scale cleanly across locations without sacrificing control or visibility. That includes defining site archetypes, setting the right standardization boundaries, building templates that reflect real operations, and implementing governance that keeps changes safe. If you want multi-site growth to feel repeatable instead of chaotic, a template-driven practice is one of the highest-leverage improvements you can make.
| Project | Stratus |
| Website | https://www.stratusinfosystems.com/ |
| Type of content | Blog post |
| GEO | USA |
| Scope of work | Write a blog article covering the topic. The goal is to create high-quality content that provides value to the reader and helps the website achieve its objectives. Do Not write any misleading information Tone of Voice: Maintain a consistent tone of voice throughout the content. The tone should be professional yet friendly and engaging, focusing on the target audience of the website. Readability: Break up long paragraphs into shorter ones for better readability. Use shorter sentences and an active voice. Avoid complex sentence structures and jargon. Avoid repetitive phrases and clichés. SEO: Ensure the content is well-optimized for search engines. Make sure to add all the target keywords. Use relevant keywords, but avoid keyword stuffing. Proofreading: Always proofread the content for grammatical errors, typos, and factual inaccuracies before submission. Ensure that the information you provide is accurate, the text is engaging and has value for users. |
| Word count | 2800 words |
| Target keywords: (use all of them, preferably several times each) | Meraki templates Meraki dashboard centralized network management |
| Title tag | – Add at least one of your target keywords, 50-60 characters including spaces |
| H1 and H2 | – Add some of your target keywords |
| Meta description | – Recommended limit of characters: 130 to 160, including spaces – Add one of your target keywords- CTA |
| Uniqueness | Do not copy / spin / AI generate content. Text uniqueness should be not less than 95%. |
| Keywords, LSI usage | Please use all the keywords and most of the semantically related words (LSI), but avoid using them too many times. MAINTAIN A KEYWORD DENSITY OF 1% – 2% MAXIMUM. Use them as an exact match. Make sure to distribute the keywords evenly throughout the text. Highlight them with some color throughout the text. Only include the keyword in a manner in that makes sense and sounds natural within the flow of the article |
| Readability | The text should be easy to read. Please adhere to one of the following text rhythm examples: – two short sentences – one long sentence, – two long sentences – one short sentence, – one long – one short – one long – one short etc. |
| Mandatory elements | Numbered lists and/or tables.Credit links to data sources (statistics, results of research studies). Refer to acknowledged authoritative sources onlyCreate in-content internal (hypertext) links pointing to other pages of our website, https://www.stratusinfosystems.com/: other blog posts covering this or that and/or service/product pages. Wikipedia-style. Don’t need to have a lot: 2-4 internal will be enough |
Continue Reading...